Does ZTNA replace VPN?
Summary:
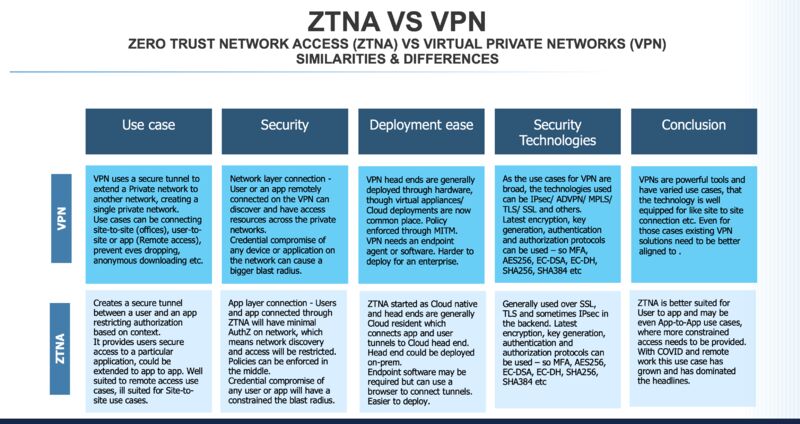
In this article, I will be discussing the differences between Zero Trust Network Access (ZTNA) and Virtual Private Networks (VPNs). Specifically, I will explore the advantages of ZTNA over VPNs, the technologies that are replacing VPNs, and the future of VPNs in the cybersecurity landscape.
Main Thought:
ZTNA is a modern security strategy that offers improved visibility, control, and performance compared to traditional VPNs. While VPNs provide a level of connectivity, they lack the advanced features and capabilities of ZTNA. ZTNA is specifically designed to meet the demands of remote work, speed, performance, and security.
Key Points:
1. VPNs route traffic through multiple servers and a central point, causing latency. ZTNA solutions connect users directly to applications, reducing latency.
2. Two common alternatives to VPNs are Software-Defined WAN (SD-WAN) and Secure Access Service Edge (SASE). These technologies provide more efficient and optimized routing of encrypted traffic.
3. VPNs only secure access to the network perimeter, while ZTNA solutions leverage multi-factor authentication and micro-segmentation for fine-grained access controls.
4. Gartner predicts that ZTNA will replace VPNs entirely by 2025, as it is the fastest-growing form of cybersecurity.
5. ZTNA can be configured as an Always-On VPN using Traffic Filters, allowing administrators to apply fine-grained access control.
6. Unlike VPNs, which provide direct access to corporate LAN endpoints, ZTNA provides access only to authorized applications and services.
7. Fortinet is among the top ZTNA vendors and has shown significant revenue growth in the market.
8. While VPNs can protect data through encryption, technologies like DNS-over-HTTPS and The Onion Router (Tor) offer alternative secure solutions.
Questions and Answers:
1. Does zero trust replace VPN?
Replace VPN with Zero Trust Strategy
2. What is the difference between Forticlient ZTNA and VPN?
VPNs route traffic centrally, causing latency, while ZTNA connects users directly to applications, reducing latency.
3. What technology is replacing VPN?
SD-WAN and SASE are common alternatives that provide more efficient routing of encrypted traffic.
4. What is the difference between ZTNA and SSL VPN?
ZTNA offers fine-grained access controls, while SSL VPNs only secure access to the network perimeter.
5. Will Gartner zero trust replace your VPN by 2025?
Gartner predicts that ZTNA will replace VPNs entirely by 2025.
6. Is ZTNA always on VPN?
ZTNA can be configured as an Always-On VPN with Traffic Filters.
7. Which feature or principle differentiates ZTNA and VPN?
ZTNA provides access to authorized applications and services, while VPNs provide direct access to corporate LAN endpoints.
8. Is Fortinet the fastest-growing ZTNA vendor?
Fortinet is among the top global ZTNA vendors, with significant revenue growth.
9. Is a VPN not needed anymore?
New technologies like DNS-over-HTTPS offer alternatives to VPNs but combining VPN and HTTPS is recommended for increased privacy protection.
10. Is there a better solution than VPN?
The Onion Router (Tor) network provides secure encryption to protect user data.
11. Do I need VPN if I have SSL?
Combining VPN and HTTPS is recommended for increased privacy protection.
12. What is the most secure VPN authentication method?
VPNs that use AES encryption are considered the most secure.
In conclusion, ZTNA offers significant advantages over traditional VPNs in terms of visibility, control, and performance. VPNs are being replaced by more efficient technologies like SD-WAN and SASE. However, VPNs still serve an essential role in the cybersecurity toolkit, especially when combined with HTTPS and used on public networks.
Does zero trust replace VPN
Replace VPN with Zero Trust Strategy
While VPN services do offer a level of connectivity, zero trust is specifically designed to meet modern needs for visibility and control as well as critical business demands such as remote work, speed, performance, security and more.
What is the difference between Forticlient ZTNA and VPN
VPNs route traffic through multiple servers and then through a central point in the corporate data center, which can cause latency in the connection. ZTNA solutions, however, connect users to applications directly without having to transmit data through that central point, which reduces latency.
Cached
What technology is replacing VPN
Two of the most common choices are software-defined WAN (SD-WAN) and Secure Access Service Edge (SASE). SD-WAN is designed to be a more efficient alternative to the VPN. Instead of implementing point-to-point connectivity, SD-WAN provides optimal routing of encrypted traffic between a network of SD-WAN appliances.
What is the difference between ZTNA and SSL VPN
VPNs only secure the access to the network perimeter. ZTNA solutions leverage a range of technologies—such as multi-factor authentication, identity federation, and micro-segmentation—to provide fine-grained access controls and ensure that only trusted users and devices can access network resources.
Will Gartner zero trust replace your VPN by 2025
Gartner believes that #zero-trust network access (#ZTNA) is the fastest-growing form of cybersecurity, will grow by 31% in 2023, and will replace #VPNs entirely by 2025. The study showed that zero trust network access is the security framework of the future and will replace virtual private networks by 2025.
Is ZTNA always on VPN
ZTNA can be configured with Always On VPN using Traffic Filters. With Traffic Filters, administrators can apply fine-grained access control for VPN traffic based on a combination of the following. Protocol (TCP, UDP, IP, etc.)
Which feature or principle differentiates ZTNA and VPN
How Is ZTNA Different from VPN Unlike VPNs, which provide direct tunneled access to an endpoint on a corporate LAN, ZTNA provides access only to explicitly authorized applications and services.
Is Fortinet the fastest growing ZTNA vendor
In fact, according to the latest Gartner report on enterprise network equipment market share, Fortinet is among the highest five global ZTNA vendors, with the fastest growing revenue of any vendor quarter-over-quarter from 4Q21-1Q22 and year-over-year from 1Q21-1Q22.
Is a VPN not needed anymore
"You're telling third parties — including your ISPs, their partners, and/or the operators of Wi-Fi networks that you're connected to — what websites and apps you use," ExpressVPN Vice President Harold Li said. However, new technology called DNS-over-HTTPS can put a stop to that — and you don't need a VPN to use it.
Is there a better solution than VPN
The Onion Router
The Onion Router (Tor) network protects user data by encapsulating the data in multiple layers of secure encryption — using the Onion Protocol — as it routes the data from sender to receiver. The Tor process ensures that a user's identity is protected from ISPs and advertisers.
Do I need VPN if I have SSL
The bottom line is that, although VPN and HTTPS can protect your data through encryption, they shouldn't be regarded as exclusive. In other words, not only is it good to combine HTTPS and VPN for increased privacy protection, but it's also recommended that you do so, especially on public, insecure networks.
What is the most secure VPN authentication method
All VPNs use encryption, but the quality of the encryption depends on which VPN protocol is used. OpenVPN, IKEv2, and L2TP support AES encryption, considered the gold standard, while WireGuard uses ChaCha20, which is also secure. PPTP uses the least secure encryption standard, MPPE.
Is VPN necessary in 2023
While more advanced cybersecurity solutions are becoming available, a business VPN is still an essential part of your security toolkit in 2023. It provides you with a safe, reliable way to access the internet, shield your data from prying eyes, and comply with security and privacy regulations.
Do I need a VPN in 2023
We strongly recommend using a good VPN for everyday use as well as for work, particularly if your work involves handling sensitive information. At CNET, we rigorously test each virtual private network across major platforms to find the ones that provide exceptional privacy, reliability, speed and value.
What is the purpose of ZTNA
Authentication and Access – The primary use for ZTNA is to provide a highly granular access mechanism based on a user's identity. Where IP-based VPN access offers broad access to a network once authorized, ZTNA offers limited, granular access to specific applications and resources.
What is the advantage of ZTNA
ZTNA allows users to access applications without connecting them to the corporate network. This eliminates risk to the network while keeping infrastructure completely invisible. Managing ZTNA solutions is easy with a centralized admin portal with granular controls.
Who is the market leader in ZTNA
Forcepoint: A Market Leader in Zero Trust Network Access
Forcepoint ZTNA provides Zero Trust remote access to private apps from anywhere, enabling advanced control over data in use across managed or unmanaged devices.
Are VPNs becoming illegal
While no specific law banning VPNs exists, the government is known to hack and eliminate content that it deems a threat to national security or public order. Individuals caught using VPNs to access restricted content may face severe penalties, such as fines worth $1,300.
Why would you disable VPN
Some reasons you might turn your VPN off
Turning off your VPN could also help diagnose some network issues. And if you're traveling to a country where VPN use is illegal or regulated, turning your VPN off could help keep you out of trouble.
Why replace VPN
VPN degrades network performance
Increasingly, the hub-and-spoke topology of VPN systems adds to network performance issues. VPN gateways concentrate all remote traffic through the private network even when the final destination is a cloud service. Data returning to the user also passes through the gateway.
What is the number 1 VPN service
ExpressVPN retained CNET Editors' Choice Award for best overall VPN after its 2023 review. It maintains its position among other virtual private network services thanks to its dedication to privacy and strong speeds. Surfshark is a close second among our picks.
Is a VPN necessary in 2023
Ultimately, a VPN is a necessary and valued tool in 2023. It completely secures your private and personal information and prevents your data from getting into the hands of third parties who can use this information against you. For such reasons, it's recommended to keep your VPN on for most if not all of the time.
What is the disadvantage of SSL VPN
The advantages of using SSL VPN are that it is more secure than a traditional VPN, and it is also easier to set up and use. The disadvantages are that it can be slower than a traditional VPN, and it may not work with all web browsers.
Is there anything more secure than a VPN
Tor is better than a VPN for the following: Online anonymity: It's almost impossible to trace a Tor connection back to the original user. You can safely visit a website without leaving any identifying evidence behind, whether on your device or the website's server.
What are two VPN authentication options
IPSec VPN supports two main modes of authentication: pre-shared key (PSK) and public key infrastructure (PKI). PSK is a simple and common method that uses a secret password or passphrase that both devices share and use to generate encryption keys.